Public Key vs Private Key – How Secure is Your Wallet?
Bitcoin is a digital currency that doesn’t exist physically. But you can still buy, sell and store it in your digital wallet. What makes it possible? And, what are public keys and private keys? A combination of the sender’s private key, and the recipient’s public key is what makes a Bitcoin transaction possible.
Bitcoin utilizes peer-to-peer technology. Money can be transferred from one individual to another directly, without the involvement of any bank. All transactions are recorded on a public ledger. Anyone who has a Bitcoin wallet can send and receive Bitcoins electronically through a PC, smartphone or web app.
Table of Contents
What is a Private Key?
Bitcoin is well-known as an electronic cash system, but underneath it all runs a secure messaging system built on the Internet. Instead of relaying emails, texts, or web pages, the Bitcoin network processes value-transfer messages called transactions. Private keys help authenticate these messages and identify each other.
Your private key is a randomly generated string (alphanumeric), allowing BTC to be spent. A private key is always mathematically related to the crypto wallet address, but is impossible to reverse engineer thanks to a strong encryption code base.
A private key is a secret number generated to allow individuals to spend their coins. When users are issued a Bitcoin address, they are also issued a Bitcoin private key. It is usually a 256-bit number and since it is the golden ticket that allows an individual to spend his or her coins, it needs to be kept safe and secure.
The private key is a secret sign that is used to decrypt the exchange message. In the traditional method, a secret key is shared within communicators to enable encryption and decryption of a message. But if the key is lost, the system becomes invalid. To avoid this weakness, PKI (public key infrastructure) came into force where a public key is used along with the private key. PKI enables internet users to exchange information in a secure way with the use of a public and private key.
In order to create a transaction, you need to import your private key. However, some wallets may make a transaction without the need of importing the private key. Others will require the private key to be swept. When private keys pass through the procedure of sweeping, a transaction will be broadcast to another address, which will include the balance.
How to Import a Bitcoin Private Key?
How does one import a Bitcoin private key? One of the methods includes the use of blockchain.info. This online tool assists users to import private tokens easily. This is achieved through their wallet service which is referred to as a hybrid ewallet. Since it is an online tool, it doesn’t store your wallet information. This is kept on your browser as an encrypted file. You are required to issue your password or alias so as to access your account. BIPS also allows the importation of private tokens easily by simply allowing the user to either type the key manually from the paper wallet or scan it using a QR reader app through a smartphone’s camera. Other private key import providers include Mycelium which provides an Android app. The app allows one to either scan the code from the paper wallet or by use of cold storage.
Why Is It Important to Keep Your Private Key in a Safe Place?
Any valid transaction bearing a valid signature will be accepted by the Bitcoin network. At the same time, any person in possession of a private key can sign a transaction. These two facts taken together mean that someone knowing only your private token can steal from you.
Many avenues are open to thieves who steal private tokens. Two of the most popular are storage media and communications channels. For this reason, extreme caution must be taken whenever storing or transmitting private keys.
Software wallets usually store private tokens in a “wallet file” on the main hard drive. Wallets often place this file in a standard, well-known directory, making it an ideal target for Bitcoin-specific malware.
To counter this threat, software wallets offer an option to encrypt the wallet file. Any attacker gaining access to your wallet file would then need to decrypt it. The difficulty of decryption depends on the quality of the encryption and strength of the password being used. Wallet files can be encrypted on many software wallets by adding a password.
What is a Public Key?
As mentioned earlier, there is also a public key. This causes some confusion, as some people assume that a Bitcoin wallet address and the public key are the same. That is not the case, but they are mathematically related. A Bitcoin wallet address is a hashed version of your public key.
A public key is obtained by subjecting a private token to a set of mathematical operations defined in a set of standards known as Elliptic Curve Cryptography (ECC). Whereas a private sign is an integer, a public key is a 2D coordinate composed of two integers. To make a public key easier to process, it can be transformed into a single value. One approach appends the y-coordinate to the x-coordinate. This technique produces an “uncompressed” key. A “compressed” key uses only the x-coordinate with a symmetry flag.
A Public key uses asymmetric algorithms that convert messages into an unreadable format. A person who has a public key can encrypt the message intended for a specific receiver. Only the receiver with the private token can decode the message, which is encrypted by the public key. The key is available via the public accessible directory.
Bitcoin Address
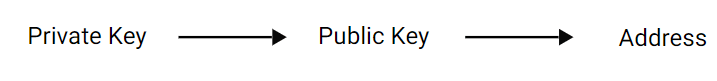
A private sign, which is just a number such as 42, can be transformed mathematically into a public key. A public token is then transformed into an address. Each of these steps is irreversible.
An address can’t generate a public key, nor can a public key generate a private key. This relationship is known as a mathematical trapdoor — a function that’s easy to perform in one direction, but practically impossible to perform in the opposite direction.
An address results from applying a multi-step transformation to a public key. This results in a string of text and digits, usually starting with the number “1”.
Notice that no network is needed at any point in the generation of a private sign or the corresponding address. Every computer on the Bitcoin network knows about the mathematical relationship between public and private signs. This enables each participant to select private keys and sign transactions independently of the Bitcoin network.
Encryption
Bitcoin solves problems through a system called public key cryptography. This system uses two pieces of information to authenticate messages. A public key identifies a sender or recipient, and can be distributed to others. A private key creates an unforgeable message signature. Public and private keys are mathematically linked through a signature algorithm, a mathematical procedure for creating identities, signing messages, and validating signatures.
Public-Key Encryption
Public-key encryption, as opposed to secret-sign encryption, consists of a pair of keys – the public, which is used to encrypt a message and the private, which is subsequently used to decrypt the cipher message.
Each private sign has only one matching public key. A message encrypted with the public key can only be decrypted with the related private sign.
The public key is available to everyone, while the private sign is only known to the wallet holder. There is never a requirement to share a secret sign via an insecure channel.
Algorithms
There are 2 broad classes of algorithms – symmetric and asymmetric. Symmetric algorithms use the same sign for both encryption and decryption. Asymmetric algorithms, such as public/private key cryptography, use one sign for encryption and a different, though mathematically related sign for decryption.
Asymmetric encryption is a technique that allows anyone to send encrypted messages to a receiver. It is based on cryptographic algorithms for generating matching pairs of public/private keys such that the private token can’t be guessed from the public key.
The public key is then published using techniques such as digital certificates. The private key is configured in encryption-enabled software and kept secret.
Symmetric encryption is based solely on private signs. For example, symmetric encryption may be used to encrypt data in storage. It is also used in communications by sharing private tokens between endpoints.
In many cases, asymmetric encryption is used to initialize a session and exchange private tokens. Then communication is encrypted with symmetric encryption. This is done because symmetric encryption is faster than asymmetric encryption.
One-Way Functions
The concept of encrypting a message with one key and not being able to decrypt it with the same sign is based on one-way functions. As the name suggests, the characteristic of a one-way function is that it is not reversible other than with a trial and error approach.
This can be achieved if there is an infinite amount of values which lead to the same result, if there is some information lost as part of the algorithm, or if the time to decrypt is immensely longer than to encrypt.
RSA Algorithm
RSA (Rivest-Shamir-Adleman), the most widely used asymmetric algorithm, is embedded in the SSL/TLS protocol which is used to provide communications security over a computer network. RSA derives its security from the computational difficulty of factoring large integers that are the product of two large prime numbers (a prime number (or a prime) is a natural number greater than 1 that has no positive divisors other than 1 and itself.). Multiplying two large primes is easy, but the difficulty of determining the original numbers from the total — factoring — forms the basis of public token cryptography security. The time it takes to factor the product of two sufficiently large primes is considered to be beyond the capabilities of most attackers, excluding nation state actors who may have access to sufficient computing power. RSA keys are typically 1024- or 2048-bits long, but experts believe that 1024-bit tokens could be broken in the near future, which is why government and industry are moving to a minimum sign length of 2048-bits.
Generate Private Key and a Public Key
- To generate a public and a private key pair, you need to pick two prime numbers p = 17 and q = 19.
- Multiply them together to retrieve the number n = 323.
- Pick another prime e = 7.
- Calculate the value d. This is done by working out the following equation:
e* d mod ((p – 1) * (q – 1)) = 1
7 * d mod 288 = 1
d = 247
Private key
The private key is d = 247.
p and q are kept secret as well. d can only be calculated if p and q are known.
Public key
The public key is formed by n and e:
n = 323
e = 7
Note that n is the product of two prime numbers. It can only be decomposed into p and q. If p and q are large enough then it is de-facto impossible.

Digital Signatures
Digital signatures are based on asymmetric cryptography and can provide assurances of evidence of origin, identity and status of an electronic document, transaction or message, as well as acknowledging informed consent by the signer. To create a digital signature, signing software (such as an email program) creates a one-way hash of the electronic data to be signed. The user’s private sign is then used to encrypt the hash, returning a value that is unique to the hashed data. The encrypted hash, along with other information such as the hashing algorithm, forms the digital signature. Any change in the data, even to a single bit, results in a different hash value. This attribute enables others to validate the integrity of the data by using the signer’s public key to decrypt the hash. If the decrypted hash matches a second computed hash of the same data, it proves that the data hasn’t changed since it was signed. If the two hashes don’t match, the data has either been altered in some way (indicating a failure of integrity) or the signature was created with a private token that doesn’t correspond to the public key presented by the signer (indicating a failure of authentication).
A digital signature also makes it difficult for the signing party to deny having signed something (the property of non-repudiation). If a signing party denies a valid digital signature, their private token has either been compromised, or they are being untruthful. In many countries, including the United States, digital signatures have the same legal weight as more traditional forms of signatures.
Behind the Scenes
Besides these key pairs and a Bitcoin wallet address, your wallet also stores a separate log of all of your incoming and outgoing transactions. Every transaction linked to your address will be stored by the wallet to give users an overview of their spending and receiving habits.
Last but not least, a Bitcoin wallet also stores your user preferences. However, these preferences depend on which wallet type you’re using and on which platform. The Bitcoin Core client, for example, has very few preferences to tinker around with, making it less confusing for novice users to get the hang of it.
Your wallet generates a “master” file where all of the preceding details are saved. For computer users, that file is called wallet.dat. It’s saved on a Windows machine, for example, in the C:\User\Yourname\Documents\AppData\Roaming\Bitcoin\folder. Make sure to create one or multiple backups of this wallet.dat file on other storage devices, such as a USB stick or memory card. The wallet software will let you import a wallet.dat file in case your previous file is damaged or lost, restoring your previous settings, including any funds associated with your cryptocurrency wallet address.
Summing up
Private and Public Keys are part of encryption that encodes information. Bitcoin is secured through digital message signatures created with a unique private token. This single point of access places a very high value on the secure generation, use, and storage of private tokens.
Public and Private token pairs help to encrypt information that ensures data is protected during transmission. What’s the difference between a public and a private key? In a nutshell, you can share your public address with others, but keep your private sign in a secure place and never show to anyone.
| Public Key | Private Key |
| A published key that can be used to send a secure message to a receiver. | A secret key that can be used to decrypt messages encrypted with the corresponding public or private key. |
| Asymmetric Encryption | Asymmetric Encryption Symmetric Encryption |